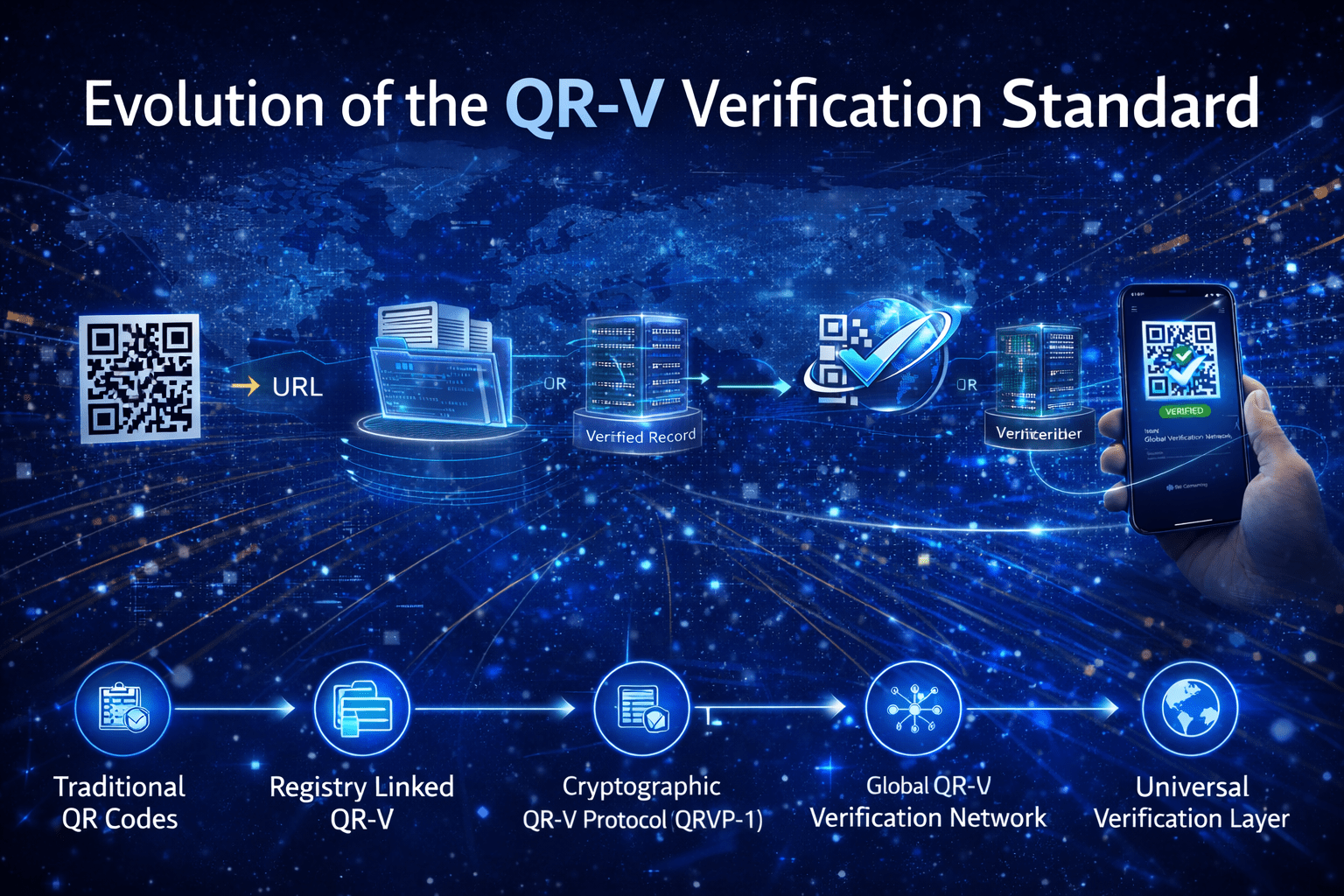
Evolution of the QR-V Verification Standard
The QR-V™ standard represents the transition from simple QR codes into a global verification infrastructure capable of authenticating digital and physical artifacts through registry-anchored records and cryptographic validation. The system introduces a verification layer similar to how DNS resolves domains or HTTPS secures web traffic.
Below is the conceptual evolution represented in the banner.
Phase 1 — Traditional QR Codes (Static Links)
Era: Early QR adoption
Characteristics:
- QR codes contain static URLs or text
- No authentication or trust validation
- Easy to copy, replace, or redirect
- Widely used for:
- marketing
- tickets
- product packaging
- payments
Security problems:
- QR phishing
- counterfeit products
- fake certificates
- cloned tickets
This stage represents linking, not verification.
Phase 2 — Registry-Linked QR (QR-V Generation 1)
QR-V introduces the first major transformation:
QR codes become verification pointers.
Instead of storing a webpage link, the QR stores a QR-V identifier.
Example format:
QRV://registry/type/objectID
Example:
QRV://ino/member/M000000001
When scanned:
Scanner
↓
Verification Node
↓
Registry Database
↓
Verification Response
The registry returns the authoritative record.
Key capabilities:
- issuer verification
- record integrity
- timestamp validation
- ownership confirmation
Phase 3 — Cryptographic QR-V Protocol (QRVP-1)
QR-V evolves into a formal Internet-style protocol.
Core components:
Identifier Layer
QRV://registry/type/objectID
Resolution Layer
Locates the correct registry.
Verification Layer
Validates signatures and hashes.
Registry Layer
Stores canonical verification records.
Response Layer
Returns validation results.
The verification process includes:
- SHA-256 hashing
- Ed25519 digital signatures
- revocation lists
- verification APIs
These security requirements ensure records cannot be forged.
Phase 4 — Global QR-V Verification Network (GQVN)
The protocol expands into a network infrastructure:
Network components
- Registries
- Verification nodes
- Client scanners
Architecture:
Scanner
↓
Verification Node
↓
Registry
↓
Cryptographic Validation
↓
Verified Response
Capabilities:
- real-time verification (<1 second target)
- distributed registries
- institutional issuance
- revocation monitoring
This creates a global verification fabric.
Phase 5 — Universal Verification Layer
At full scale, QR-V becomes a global verification standard.
Possible sectors:
Identity
- government IDs
- memberships
- passports
- digital credentials
Education
- diploma verification
- certificates
- professional licenses
Finance
- bonds
- asset certificates
- securities
Supply Chain
- product authentication
- anti-counterfeiting
- origin verification
Documents
- legal records
- contracts
- property titles
Healthcare
- credentials
- pharmaceutical authenticity
Final Evolution
Traditional QR Code
QR → URL
QR-V
QR → Identifier → Registry → Cryptographic Verification
The shift is from linking information to verifying truth.
Strategic Impact
If executed globally, QR-V could become:
- a verification layer for the physical world
- a trust infrastructure for digital credentials
- a registry-based authentication system
Comparable infrastructure categories include:
- DNS (domain resolution)
- HTTPS (web security)
- Certificate Authorities (TLS trust)
QR-V would operate in the same class as a verification protocol for real-world objects.
There are no comments